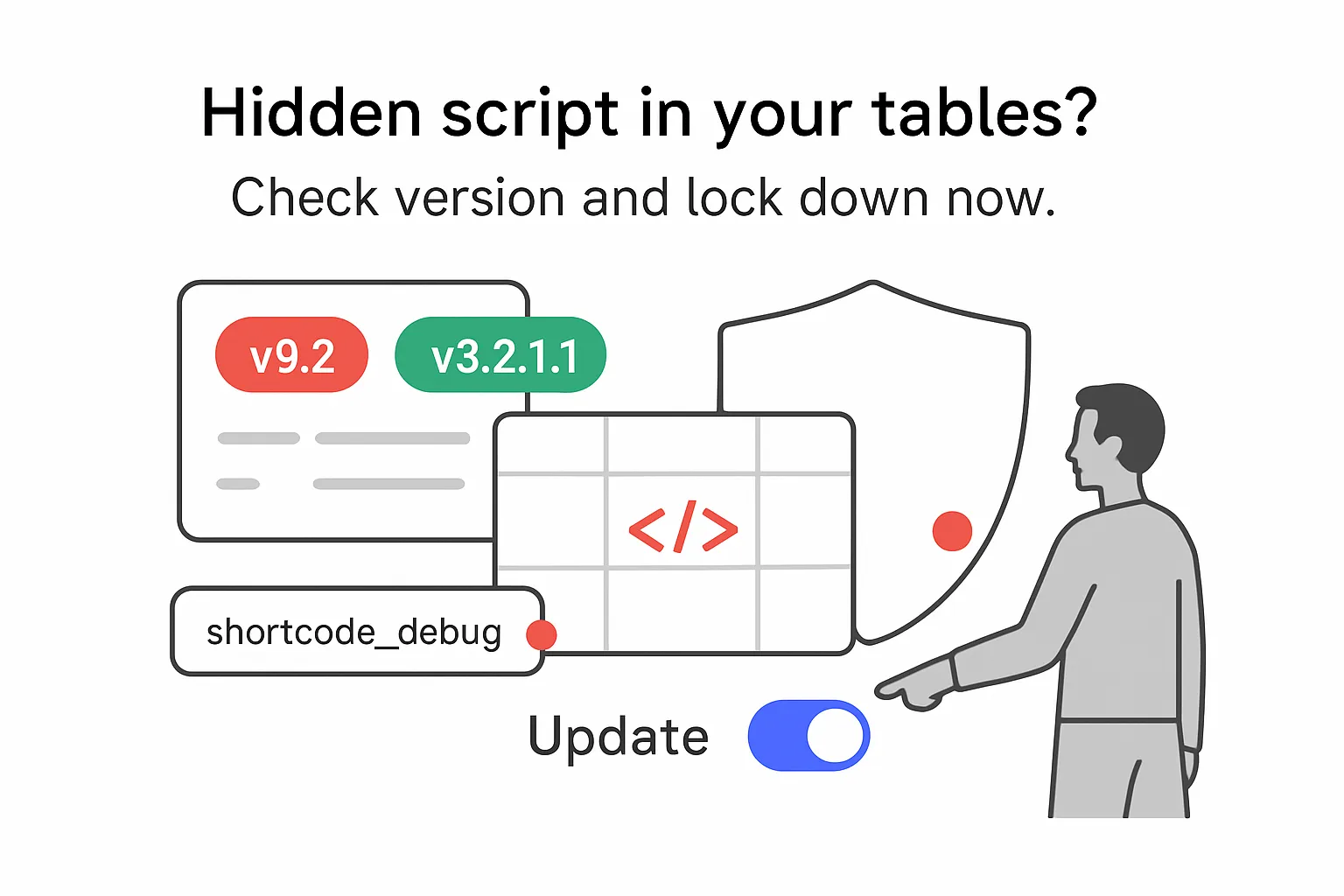
Wordfence disclosed a stored cross-site scripting (XSS) vulnerability in the TablePress WordPress plugin affecting versions up to and including 3.2. The developer released version 3.2.1 with a fix, and site owners should update promptly.

TablePress WordPress Plugin Vulnerability
According to Wordfence's advisory, insufficient input sanitization and output escaping around the shortcode_debug parameter allow authenticated users with contributor-level or higher privileges to inject stored XSS payloads. These scripts execute when a visitor loads an affected page. TablePress is widely used to build sortable, searchable tables in WordPress.
Key Details
- Vulnerability type: stored cross-site scripting via the "shortcode_debug" parameter.
- Affected versions: up to and including 3.2.
- Exploitation requires authenticated contributor-level access or higher.
- Impact: stored scripts can run when an affected page is viewed.
- Fixed version: 3.2.1, available on the WordPress Plugin Directory.
- Active installations: 800,000+ per the WordPress.org listing.
Background Context
TablePress enables site owners to create and manage tables in WordPress without coding. Features include sorting, pagination, and search.
Stored XSS occurs when untrusted input is saved and later rendered without proper escaping. Wordfence attributes this case to insufficient sanitization and escaping in the affected parameter.




.svg)