A vulnerability in the Formidable Forms WordPress plugin, disclosed by Wordfence, allows unauthenticated attackers to misreport Stripe payments on affected sites.
The flaw, tracked as CVE-2026-2890, impacts Formidable Forms versions up to and including 6.28. Wordfence reports that a fix is available in version 6.29 and later.

Key Details
Formidable Forms is a drag-and-drop form builder used on more than 300,000 WordPress sites, according to its plugin listing. Site owners use it to create contact, registration, survey, and payment forms that integrate with gateways such as Stripe and PayPal.
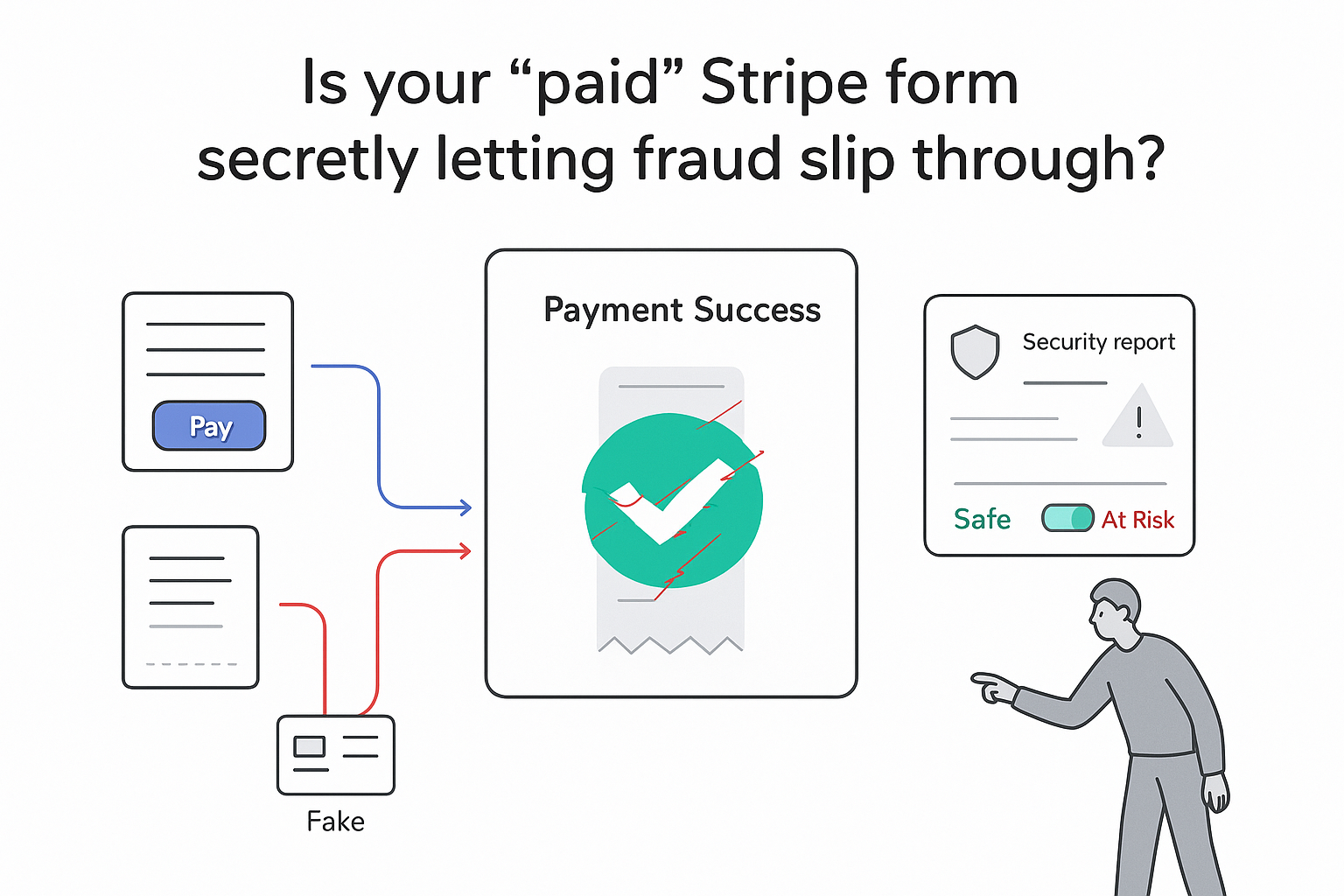
- Wordfence identifies the issue as a payment integrity bypass affecting Stripe Link one-time payment handling.
- The flaw allows reuse of a valid Stripe PaymentIntent from a low-value payment to mark a higher-value payment as complete.
- Attackers do not need an account on the target site, since the vulnerable process is accessible without authentication.
- According to Wordfence, the
handle_one_time_stripe_link_return_urlfunction marks payments complete based only on PaymentIntent status. - The
verify_intent()function reportedly confirms only that the client secret belongs to a user, without linking it to a specific form entry. - The vulnerability is tracked as CVE-2026-2890 and has a CVSS 3.1 base score of 7.5, rated High.
- All Formidable Forms versions up to and including 6.28 are listed as affected in the Wordfence advisory.
Background Context
According to Wordfence, the Stripe Link return handler does not compare the charged amount against the amount expected by the form. As a result, a PaymentIntent created for a smaller charge can be reused during a separate transaction that should cost more.
The advisory notes that the plugin treats any successful PaymentIntent status as evidence of payment completion for the related form submission. Because the amount and specific action are not validated, attackers can cause higher-priced entries to be recorded as paid in Formidable Forms, even though Stripe processed only the smaller original charge.
The vulnerability does not grant remote code execution or direct server control. It affects transaction records by allowing goods or services to appear paid within the site workflow without matching Stripe charges. Wordfence states that version 6.29 of Formidable Forms contains a patch that addresses the described validation issues.
Wordfence attributes the issue to missing authorization checks combined with insufficient binding of PaymentIntents to individual forms or actions. The plugin continues to be available through the official WordPress plugin repository, where its active installation count exceeds 300,000. Wordfence notes that it recommends updating Formidable Forms to version 6.29 or newer.
Source Citations
Information about the vulnerability, impact, affected versions, and patch originates from Wordfence's public disclosure and advisory. Installation figures and plugin usage details are drawn from the official WordPress plugin directory.




.svg)